An algorithm for Peruvian counterfeit Banknote Detection based on Digital Image Processing and SVM
Volume 6, Issue 1, Page No 1171–1178, 2021
Adv. Sci. Technol. Eng. Syst. J. 6(1), 1171–1178 (2021);
 DOI: 10.25046/aj0601132
DOI: 10.25046/aj0601132
Keywords: Counterfeit, Detection, SVM, Digital Image Processing, Banknote
In this work we propose an algorithm for Peruvian counterfeit banknotes detection. Our algorithm operates in banknotes with 50, 100 and 200 soles denominations that were manufactured from 2009 onwards. This algorithm offers an automatic diagnosis based on digital image processing and support vector machines (SVM). Current Peruvian counterfeit detection systems are specially designed to analyze relevant characteristics in dollars and euros. Then, some counterfeiters can fool these systems. We made our detection system robust because we focus on the image acquisition and the segmentation of intaglio marks engraved over the banknotes. After segmentation, we applied embossing and Sobel filters followed by an aperture morphological operation to obtain special characteristics that were then classified by an SVM. We have validated our methodology using real and fake banknotes from a dataset of 240 samples provided by Central Reserve Bank of Peru (BCRP). Our final identification accuracy was 96.5%.
1.Introduction
In order to properly introduce the proposed algorithm, it’s been divided into three sections: motivation and incitement, literature review and contribution.
1.1. Motivation and incitement
In Peru, counterfeiting money is a well-known fraud method. In fact, according to the Central Office Against Counterfeiting Money from Peru, the amounts of fraudulent banknotes have reached millionaire quantities (Oficina Central de Lucha contra la Falsificación de Numerario – OCN – Peru: “Principales operativos contra la falsificación” Available: http://www.ocn.gob.pe). As a result, the annual report of the United States Secret Service, an entity with which the Peruvian National Police works together to combat national and foreign banknote counterfeiting, places Peru as the main banknote counterfeiter country worldwide, surpassing other South American countries such as Colombia , which had this title before.
In Peru, this type of practice is especially problematic and constitutes an attack on society, because it makes people to lose trust on currency in circulation which increases money transaction time. Even worse, this distrust in Peruvian money hurts the economic growth and, in the long term, it could also lead to inflation because, as there is more money circulating than the amount the government can handle, people purchasing power increases, which would turn into an increase in prices. Finally, this ends up affecting the economy of any person or any company that receives the fradulent banknotes, especially when those banknotes are the ones with the highest denomination.
In this context, some enterprises offer solutions in the form of counterfeit banknote detectors. However, most of these detectors are based on foreign banknote manufacturing technologies, such as the “Elwic BC 3500 UV / MG next-generation banknote counter” or “PREZZOPAZZO DST-38D banknote detector”, which use verification parameters such as magnetism, infrared or banknote thickness, all of which have already been fooled by Peruvian banknotes counterfeiters.
A common method used by scammers is to discolorate low-denomination banknotes (i.e. 10 or 20 soles banknotes), and then overprint them with high-denomination banknote values (i.e. 50, 100 or 200 soles banknote values). These overprints can be of very high detail so they successfully fool the aforementioned verification parameters used by commercial detectors. However these type of techniques are less common on lower denomination banknote (10 and 20 soles) as they would be less cost effective.
Our algorithm focuses on intaglio marks which are distinctive for Peruvian banknotes and whose imitations have not reached such a high level of sophistication.
The focus of the algorithm is on the higher denomination banknotes (50, 100 and 200 soles) since these are the more commonly counterfeited and the more damaging to the victims.
Some other commercial detectors are aimed to serve more as inspection tools for the user, using ultraviolet lights or magnifying glasses as is in the case of “Elwic Professional Banknote Detector IRD-2200” or the “Anizun Magnifying glass mini microscope”. These solutions do not provide a clear detection verdict. Rather, they are based on users’ prior knowledge of the distinctive marks and details that a legitimate banknote must have. By relying on the human senses, these methods have an intrinsic error. Furthermore, counterfeiters are capable of mimicking several of the most distinctive characteristics of authentic banknotes, such as fluorescent markings or some images that give the illusion of being seen against the light (Arjowiggins Security. “Security features: Watermarks, security fibres and security threads” Available: https://securitypapers.arjowiggins.com). Compared to these detection tools, our method offers a clear and readable verdict on the denomination and legitimacy of the analyzed banknote.
Another common counterfeit technique used in Peruvian banknotes is the removal of security bands from 100 and 200 soles banknotes. These bands are manually removed from a legitimate banknote and placed on a falsified one, then the legitimate but damaged banknote can be exchanged for a new one in banks. This way, counterfeiters have a fake one with a security band that would pass even a meticulous examination. Our algorithm can tackle this problem as it uses banknotes intaglio marks that cannot be removed and placed in falsified ones.
1.2. Literature review
We reviewed various scientific publications related to banknote analysis.
For example in [1] and [2] the authors tackled the automatic banknote denomination recognition problem by using digital image processing techniques. However in our proposed algorithm we not only determine banknote denomination but, in addition, perform a procedure aimed to identify the veracity of the banknote by analyzing intaglio marks with digital image processing techniques.
On the other hand, in [3] and [4] the authors were concerned about banknotes veracity but did not contemplate the use of an enclosure to standardize image light conditions. In comparison, our proposed solution does use an enclosure to ensure uniform illumination across all processed training and validation images.
Publications such as [5] and [6] that are based on digital image processing techniques have some flaws, as they did not consider the use of supervised learning algorithms to solve the classification task. On the contrary, our proposed solution uses a support vector machine (SVM) to tackle the classification problem after a training process performed with labeled images.
Some recent publications include the use of artificial intelligence [7] and deep learning [8] to detect counterfeit currency. However, these algorithms were designed and tested to work on other currencies such as dollars, euros, etc. Its performance on peruvian banknote has not been tested and they don’t use the intanglio marks as a classification parameter, which is the most difficult detail to forge.
Likewise, convolution techniques and neural networks are used in [8] which demand a lot of computational load and therefore requires to be implemented in hardware boards such as Jetson TX2. In contrast, we propose a low complexity algorithm that can be easily implemented on a small single-board computer (such as Raspberry Pi 3) with very satisfactory results.
1.3. Contribution and paper organization
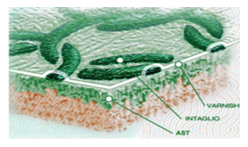
Given that intaglio marks (Banco Central de Reserva del Perú, BCRP: “Elementos de seguridad de los billetes de 100 soles”, Available: http://www.bcrp.gob.pe) are banknotes difficult-to-falsificate features we decided to design an algorithm that analyzes them (see Figure 1 for a view of some intaglio marks). In order to analyze intaglio marks we capture banknote images using a digital camera and an enclosure to guarantee proper light conditions. These images are then analyzed and enhanced using image processing techniques and a support vector machine (SVM) to determine whether the image corresponds to a legitimate or a fake banknote. Thus, our proposed system offers an automatic diagnostic on the veracity of the banknote analyzed.
Taking all these considerations into account, our methodology was able to perform a 96.5% of detection over the image dataset comprising 240 banknotes provided by the Central Reserve Bank of Peru (BCRP).
The amount of 240 samples was the result of the source of information provided by the Central Reserve Bank of Peru.
The selection of these samples had the following filters.
- The number of samples for the indicated denominations is reduced to 2 groups.
- The first group is confirmed by banknotes that did not enter into circulation, i.e., that did not deceive people.
- The second group of banknotes belongs to the group that entered circulation, i.e. the user did not detect the counterfeit banknote at the beginning.
For the validation process the second group was selected. In this case, BCRP specialists selected the banknotes that presented the greatest difficulty in detecting counterfeits. The details of the proposed algorithm, the results of the tests and the conclusions will be described in the following sections.
2. Proposed algorithm
For a better understanding, the distinctive characteristics of Peruvian banknotes will be first described and then a discussion of the main blocks of our algorithm will be presented.
 Figure 2: Intaglio marks for a (a) Fifty soles banknote, (b) One-hundred soles banknote, (c) Two-hundred soles banknote.
Figure 2: Intaglio marks for a (a) Fifty soles banknote, (b) One-hundred soles banknote, (c) Two-hundred soles banknote.
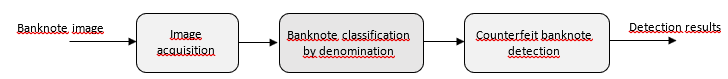 Figure 3: Block diagram of the proposed algorithm
Figure 3: Block diagram of the proposed algorithm
2.1. Banknotes characteristics
We will focus our analysis on the intaglio marks from 50, 100 and 200 soles banknotes (Banco Central de Reserva del Perú, BCRP: “Nuevos billetes de 50, 100 y 200 soles”, Available: http://www.bcrp.gob.pe). These marks can be appreciated by the human eye only if banknotes are positioned as in Figure 2 and with good illumination conditions. These marks depend on the banknote denomination, for this reason it is important to first determine the banknote denomination before proceeding with the analysis of intaglio marks.
In Figure 3 we present the block diagram of the proposed algorithm. In the following sections we will describe each block.
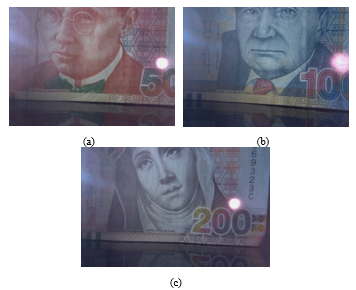 Figure 4: Sample of acquired images for (a) Fifty soles banknote, (b) One-hundred soles banknote, (c) Two-hundred soles banknote.
Figure 4: Sample of acquired images for (a) Fifty soles banknote, (b) One-hundred soles banknote, (c) Two-hundred soles banknote.
2.1. Image acquisicion
We used a closed enclosure to control light conditions, the enclosure was illuminated by a 3W white light LED. To capture the intaglio marks, every picture was taken from the right side of the banknote obverse. The sample banknotes are placed into the enclosure using mechanical guides that help with their correct and quick placement. LED lights were positioned so the area of interest would be distinguished more clearly.
A Raspberry v1 camera was used to take the picture, this camera has a CMOS OmniVision OV56476 with 5 megapixels (2592 x 1944 pixels resolution). The banknotes region of interest has RGB format (true color, 24 bits per pixel). Each primary component is defined as , and , where are the spatial coordinates.
All the computations were made by the Raspberry Pi 3B + single board computer which is compatible with the camera used and can perform all the required processing steps in less than 3 seconds with low power consumption (5 V /2.5 A). The acquired image is set to M=1644 rows and N=2592 columns.
In Figure 4 we showed 50, 100 and 200 soles banknotes taken under the described conditions.
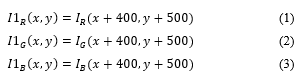
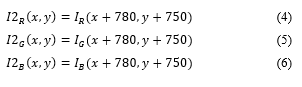
2.2. Banknote classification by denomination
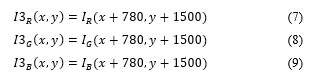
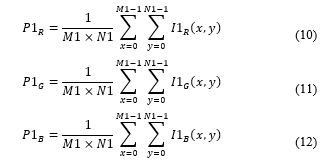
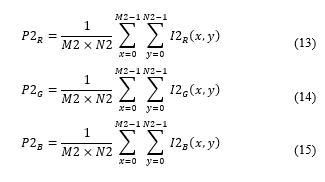
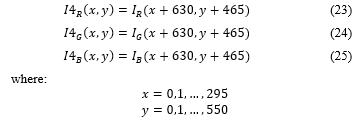
Given the captured images, we defined three regions of interest that were fixed so we can identify relevant characteristics in each banknote. These regions of interest can be expressed as:
Region 1:
![]() These regions were chosen because they allow us to differentiate between banknotes denomination by their coloration (See Fig. 5 for an example in a 200 soles banknote).
These regions were chosen because they allow us to differentiate between banknotes denomination by their coloration (See Fig. 5 for an example in a 200 soles banknote).
 Figure 5: Two-hundred soles banknote with the three regions of interest (red boxes).
Figure 5: Two-hundred soles banknote with the three regions of interest (red boxes).
We averaged color components in every region of interest as features. To compute these averages, we use the following equations:

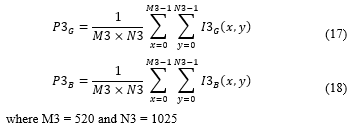 We compound this averages in a feature vector defined as:
We compound this averages in a feature vector defined as:
![]() The compound feature vector is then classified using a Support Vector Machine (SVM) with a radial basis function kernel [10]. This kernel, which is described as a Gaussian function, was chosen because of its high performance to classify nonlinear data, as it is in our case. SVM was selected as the classifier because of its better performance compared with other techniques like KNN and because of its robustness to classify nonlinear data [11]. We used 70% of the banknotes for training and 30% for testing. We obtained a 99% of accuracy in this task as will be detailed in the results section.
The compound feature vector is then classified using a Support Vector Machine (SVM) with a radial basis function kernel [10]. This kernel, which is described as a Gaussian function, was chosen because of its high performance to classify nonlinear data, as it is in our case. SVM was selected as the classifier because of its better performance compared with other techniques like KNN and because of its robustness to classify nonlinear data [11]. We used 70% of the banknotes for training and 30% for testing. We obtained a 99% of accuracy in this task as will be detailed in the results section.
2.3. Counterfeit banknote detection
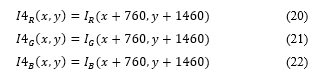
After banknote classification by denomination, we now proceed to determine if the banknote is false or legitimate. To do so, we first isolate a counterfeit detection region of interest per banknote denomination as follows:
For fifty soles banknotes:
For two-hundred soles banknotes:
 In Figure 6, we zoom in these regions of interest.
In Figure 6, we zoom in these regions of interest.
After the selection of the counterfeit detection region of interest, we compute averages in each component using the following equations:
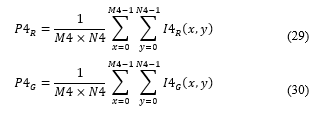
 Figure 6: Amplified regions of interest for counterfeit banknote detection in the case of a (a) Fifty soles banknote, (b) One-hundred soles banknote, (c) Two-hundred soles banknote.
Figure 6: Amplified regions of interest for counterfeit banknote detection in the case of a (a) Fifty soles banknote, (b) One-hundred soles banknote, (c) Two-hundred soles banknote.
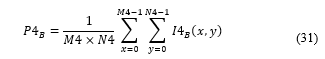 Every color component is then enhanced using an embossing filter [12] which is designed according to the banknote denomination, as is shown in equations (32), (33) and (34).
Every color component is then enhanced using an embossing filter [12] which is designed according to the banknote denomination, as is shown in equations (32), (33) and (34).
 We then obtain the filtered components , and which have highlighted textures as can be seen in Figure 7.
We then obtain the filtered components , and which have highlighted textures as can be seen in Figure 7.
 Figure 7: Results of the embossing filter in every region of interest for 50,100 and 200 soles banknotes.
Figure 7: Results of the embossing filter in every region of interest for 50,100 and 200 soles banknotes.
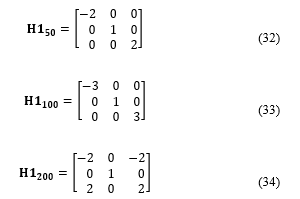
To magnify edges, we applied Sobel filters [13] over the embossing components. In the case of the one-hundred banknote, we used a sobel variation filter due to the diagonal orientation of intaglio marks in this banknote. Final sobel filters are defined in equations (35), (36) and (37).
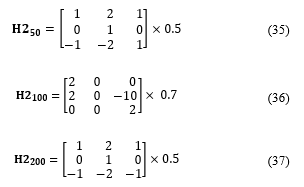 After this step, we obtain as results , and . Sobel filters are designed to sharp edges and variations [14], as we can see in Figure 8.
After this step, we obtain as results , and . Sobel filters are designed to sharp edges and variations [14], as we can see in Figure 8.
 Figure 8: Sobel filter results for 50, 100 and 200 soles banknotes.
Figure 8: Sobel filter results for 50, 100 and 200 soles banknotes.
Now, the components are binarized using a threshold that varies with the banknote denomination [15]. Since constant illumination conditions are guaranteed, constant thresholds are used for each denomination in the binarization process. The resulting components are expressed using the following equations:
For fifty soles banknotes:
![]()
 For one-hundred soles banknotes:
For one-hundred soles banknotes:
 For two-hundred soles banknotes:
For two-hundred soles banknotes:
 The binarization process allowed us to reduce information from grayscale images [16]. Instead of an 8-bit image, now we have a 1-bit image, as seen in Figure 9.
The binarization process allowed us to reduce information from grayscale images [16]. Instead of an 8-bit image, now we have a 1-bit image, as seen in Figure 9.
 Figure 9: Results from the binarization process
Figure 9: Results from the binarization process
After this, we filtered the results using the aperture morphological operation. We do this to eliminate some noisy elements and enhance visibility of objects of interest (intaglio marks) [17]. Structuring elements are designed depending on the banknote denomination as follows.
 Thus, we obtain new image components , and . Figure 10 shows some results.
Thus, we obtain new image components , and . Figure 10 shows some results.
We then apply connectivity 4 to count the number of objects in each component. The number of objects per component are denominated , y . We use these values to create a new compound feature vector as follows:
![]() This feature vector is classified using an SVM trained per each banknote denomination (i.e. we used 3 SVMs). Thus, we used independent hyperplanes to perform our classification for our 6-dimensional vector [18]. Again, we used a radial basis function kernel [11] and 70% of the banknotes for training and 30% for testing.
This feature vector is classified using an SVM trained per each banknote denomination (i.e. we used 3 SVMs). Thus, we used independent hyperplanes to perform our classification for our 6-dimensional vector [18]. Again, we used a radial basis function kernel [11] and 70% of the banknotes for training and 30% for testing.
 Figure 10: Results after aperture morphological operation using specially designed structural elements.
Figure 10: Results after aperture morphological operation using specially designed structural elements.
3. Results
In this section we present our results for the classification and detection tasks using our 240 banknote dataset which are distributed as shown in Table 1. The ground-truth veracity of the banknotes was determined by a specialist of the BCRP.
Result for the banknote classification by denomination task are presented in Table 2. As we used 70% of the data to train the SVM classifier these results correspond to the remaining 30%. To compute our performance metric we divide the number of correct results by total number of samples.
As we can see, the results from this step were almost perfect, we only had one mistake in the classification of a one-hundred soles banknote.
In Table 3 we show the results for the detection process.
Results obtained in the detection process are satisfactory. There was only one mistake on a 50 soles banknote and another one on a 100 soles banknote.
Table 1: Banknotes distribution
| Denomination | Veracity | Number of samples |
| 50 | Legitimate | 32 |
| Fake | 50 | |
| 100 | Legitimate | 40 |
| Fake | 49 | |
| 200 | Legitimate | 32 |
| Fake | 37 |
Table 2: Results for the classification process
| Denomination | Number of test samples | Correctly classified samples | Performance |
| 50 | 22 | 22 | 100% |
| 100 | 33 | 32 | 97% |
| 200 | 21 | 21 | 100% |
Table 3: Results for the detection process.
| Denomination | Number of test samples | Correctly detected samples | Percentage of correct detection |
| 50 | 25 | 24 | 96% |
| 100 | 28 | 27 | 96.4% |
| 200 | 21 | 21 | 100% |
In Tables 4, 5 and 6, we show correct and incorrect detections of the true and false banknote by denomination. In Table 4, a legitimate 50 soles banknote was incorrectly detected as false. This was caused by a deteriorated banknote that was bent on several places. In Table 5, a legitimate 100 soles banknote was incorrectly detected as false. This was caused by an incorrect insertion of the banknote on the image acquisition zone.
Table 4: Results for the 50 soles banknote detection process
| Sample\Result | Legitimate | Fake |
| Legitimate | 14 | 1 |
| Fake | 0 | 10 |
Table 5: Results for the 100 soles banknote detection process
| Sample\Result | Legitimate | Fake |
| Legitimate | 14 | 1 |
| Fake | 0 | 12 |
Table 6: Results for the 200 soles banknote detection process
| Sample\Result | Legitimate | Fake |
| Legitimate | 7 | 0 |
| Fake | 0 | 14 |
The average performance (according with Table 3) is then 97.47%. We observed that mistakes were generated because of banknote positioning problems (they were not inserted correctly or maybe the banknote was bent so its image could not be acquired correctly).
According to Table 3, the average detection performance of the proposed algorithm is 97.47%. The detection errors were mainly generated by banknote positioning problems, i.e. the banknotes were not inserted correctly or perhaps the banknote was bent, so its image could not be acquired correctly.
These problems could be solved by the use of additional hardware or by training the SVM classifier with images with these imperfections.
Finally, the total effectiveness of our algorithm (including classification and detection) is computed using the following equation:
![]() where is the percentage of correct classifications, is the percentage of correct detections given a correct classification. Table 7 summarizes our final results.
where is the percentage of correct classifications, is the percentage of correct detections given a correct classification. Table 7 summarizes our final results.
Then, the total effectiveness average is 96.5%, which are results that could improve with a bigger sample. Compared to other studies with different currencies, it reached a higher percentage than Ballado’s (95%) [6] and a lower percentage than Han’s (100%) [7].
Table 7: Total effectiveness
| Denomination | |||
| 50 | 100% | 96% | 96% |
| 100 | 97% | 96.4% | 93.5% |
| 200 | 100% | 100% | 100% |
4. Conclusions
The proposed algorithm was able to identify the denomination and veracity of Peruvian banknotes that were manufactured from 2009 onwards using the intanglio marks as a deciding factor, and support vector machines (SVM). The practical operation of this algorithm was validated by specialists from the Central Reserve Bank of Peru (BCRP). The few cases in which the algorithm failed were caused by the deteriorated state of the banknote. It is suggested not to use banknote that is ripped or folded in order to avoid missreadings.
Our automatic algorithm was efficient and can be used by any user who needs to determine the veracity of Peruvian 50, 100 or 200 soles banknotes.
The algorithm was entirely developed in Python and was embedded into a Raspberry single board computer. Additionally, does not consume high computational resources.
As we increase the number of training samples we can improve SVM performance for classification.
Conflict of Interest
The authors declare no conflict of interest.
Acknowledgment
The authors would like to thank the Research Directorate of the Peruvian University of Applied Sciences (UPC) for technical and economic support and the Central Reserve Bank of Peru (BCRP) for providing the banknotes used in this study.
- G. Ramasamy and S. Subramanian, “Identification of currency denomination using image processing,” International Journal of Advanced Research, Ideas and Innovations in Technology, 5(2), 2019.
- S. Guzmán, Detector de billetes para personas con discapacidad visual, BSc. Thesis, Universidad Tecnológica del Perú, 2012.
- D. Alekhya, G. Prabha, G. D. Rao, “Fake currency detection using image processing and other standard methods,” International Journal of Research in Computer and Communication Technology, 3(1), 2014.
- J. L. Estela, Análisis comparativo de algoritmos de reconocimiento de imágenes por descriptores de color para la identificación de billetes, BSc. Thesis, Universidad Señor de Sipán, Chiclayo, Peru, 2016.
- Abdullah M. Shoeb, Hadeer M. Sayed, Norah F. Saleh, Ehab I. Khafagy, Sameh Neji, “Software system to detect counterfeit Egyptian currency,” in International Conference on Control, Instrumentation, Communication and Computational Technologies, 2016, doi:10.1109/ICCICCT.2016.7988010.
- A. H. Ballado, J. C. Dela Cruz, G. O. Avendaño, N. M. Echano, J. E. Ella, M.E.M. Medina, B.K.C. Paquiz, “Philippine currency paper bill counterfeit detection through image processing using Canny Edge Technology,” in 8th IEEE International Conference on Humanoid, Nanotechnology, Information Technology, Communication and Control, Environment and Management (HNICEM), 2015, doi:10.1109/HNICEM.2015.7393184.
- M. Han, J. Kim, “Joint banknote recognition and counterfeit detection using explainable artificial intelligence,” Sensors, 19(16), 3607, 2019, doi.org/10.3390/s19163607.
- T. D. Pham, C. Park, D. T. Nguyen, G. Batchuluun, K. R. Park, “Deep learning-based fake-banknote detection for the visually impaired people using visible-light images captured by smartphone cameras,” IEEE Access, 8, 63144 – 63161, 2020, doi:10.1109/ACCESS.2020.2984019.
- T. Crane, “Some observations on technological developments in durable substrates,” Billeteria: International review on cash management, 5(9), 2011.
- D. Duvenaud. Automatic model construction with Gaussian processes, Ph.D. Thesis, Pembroke College, England, 2014.
- C. M. Bishop, Patter recognition and machine learning, Springer, 2006.
- S. Umbaugh, Computer imaging: Digital image analysis and processing, CRC Press, 2010.
- J. Álvarez, J. Fernández, “Procesamiento de imágenes bajo Windows CE utilizando el procesaror ARMv 4I,” ITECKNE Innovación e Investigación en Ingeniería, 8(2), 2008, doi: 10.15332/iteckne.v8i2.41.
- R. Muthukrishnan, M. Radha, “Edge detection techniques for image segmentation,” International Journal of Computer Science and Information Technology, 3(6), 2011, doi:10.5121/ijcsit.
- R. Gonzalez, R. Woods. Digital Image Processing, Pearson, 2018.
- C. Solomon, T. Breckon, Fundamentals of digital image processing: A practical approach with examples in Matlab, John Wiley & Sons, 2010.
- G. Aguilar, Procesamiento digital de imágenes utilizando filtros morfológicos, BSc. Thesis, Escuela Politécnica Nacional, Quito, Ecuador, 1995.
- C. C. Chang, C. J. Lin, “LIBSVM: A Library for Support Vector Machines,” ACM Transactions on Intelligent Systems and Technology, 2(3), 2011, doi.org/10.1145/1961189.1961199.
- Youssef Keryakos, Youssef Bou Issa, Michel Salomon, Abdallah Makhoul, "Introducing a Stress Management and Navigation System for Blind Individuals", Advances in Science, Technology and Engineering Systems Journal, vol. 10, no. 2, pp. 12–27, 2025. doi: 10.25046/aj100202
- Sarawuth Pramualsingha, Kazuo Yamamoto, RikutoTanaka, "Lightning Detection System for Wind Turbines Using a Large-Diameter Rogowski Coil", Advances in Science, Technology and Engineering Systems Journal, vol. 10, no. 1, pp. 1–6, 2025. doi: 10.25046/aj100101
- Abdennacer El-Ouarzadi, Anass Cherkaoui, Abdelaziz Essadike, Abdenbi Bouzid, "Hybrid Optical Scanning Holography for Automatic Three-Dimensional Reconstruction of Brain Tumors from MRI using Active Contours", Advances in Science, Technology and Engineering Systems Journal, vol. 9, no. 4, pp. 07–13, 2024. doi: 10.25046/aj090402
- Toya Acharya, Annamalai Annamalai, Mohamed F Chouikha, "Enhancing the Network Anomaly Detection using CNN-Bidirectional LSTM Hybrid Model and Sampling Strategies for Imbalanced Network Traffic Data", Advances in Science, Technology and Engineering Systems Journal, vol. 9, no. 1, pp. 67–78, 2024. doi: 10.25046/aj090107
- Ajla Kulaglic, Zeynep Örpek, Berk Kayı, Samet Ozmen, "Analysis of Emotions and Movements of Asian and European Facial Expressions", Advances in Science, Technology and Engineering Systems Journal, vol. 9, no. 1, pp. 42–48, 2024. doi: 10.25046/aj090105
- Toya Acharya, Annamalai Annamalai, Mohamed F Chouikha, "Optimizing the Performance of Network Anomaly Detection Using Bidirectional Long Short-Term Memory (Bi-LSTM) and Over-sampling for Imbalance Network Traffic Data", Advances in Science, Technology and Engineering Systems Journal, vol. 8, no. 6, pp. 144–154, 2023. doi: 10.25046/aj080614
- Koloud N. Alkhamaiseh, Janos L. Grantner, Ikhlas Abdel-Qader, Saad Shebrain, "Towards Real-Time Multi-Class Object Detection and Tracking for the FLS Pattern Cutting Task", Advances in Science, Technology and Engineering Systems Journal, vol. 8, no. 6, pp. 87–95, 2023. doi: 10.25046/aj080610
- Mai Ngoc Anh, "Simulation of Obstacle Detection Based on Optical Flow Images for Avoidance Control of Mobile Robots", Advances in Science, Technology and Engineering Systems Journal, vol. 8, no. 3, pp. 244–249, 2023. doi: 10.25046/aj080327
- Christoph Domnik, Daniel Erni, Christoph Degen, "Measurement System for Evaluation of Radar Algorithms using Replication of Vital Sign Micro Movement and Dynamic Clutter", Advances in Science, Technology and Engineering Systems Journal, vol. 8, no. 3, pp. 29–39, 2023. doi: 10.25046/aj080304
- Ivana Marin, Sven Gotovac, Vladan Papić, "Development and Analysis of Models for Detection of Olive Trees", Advances in Science, Technology and Engineering Systems Journal, vol. 8, no. 2, pp. 87–96, 2023. doi: 10.25046/aj080210
- Paulo Gustavo Quinan, Issa Traoré, Isaac Woungang, Ujwal Reddy Gondhi, Chenyang Nie, "Hybrid Intrusion Detection Using the AEN Graph Model", Advances in Science, Technology and Engineering Systems Journal, vol. 8, no. 2, pp. 44–63, 2023. doi: 10.25046/aj080206
- Habiba Sultana, A. H. M. Kamal, "An Efficient Way of Hybridizing Edge Detectors Depending on Embedding Demand", Advances in Science, Technology and Engineering Systems Journal, vol. 8, no. 1, pp. 63–77, 2023. doi: 10.25046/aj080108
- Roy D Gregori Ayon, Md. Sanaullah Rabbi, Umme Habiba, Maoyejatun Hasana, "Bangla Speech Emotion Detection using Machine Learning Ensemble Methods", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 6, pp. 70–76, 2022. doi: 10.25046/aj070608
- Lixin Wang, Jianhua Yang, Austin Lee, Peng-Jun Wan, "Matching TCP Packets to Detect Stepping-Stone Intrusion using Packet Crossover", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 6, pp. 13–19, 2022. doi: 10.25046/aj070602
- Rafia Akhter, Fred Beyette, "Detection of Event-Related Potential Artifacts of Oddball Paradigm by Unsupervised Machine Learning Algorithm", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 5, pp. 157–166, 2022. doi: 10.25046/aj070517
- Hassan Facoiti, Ahmed Boumezzough, Said Safi, "Computer Vision Radar for Autonomous Driving using Histogram Method", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 4, pp. 42–48, 2022. doi: 10.25046/aj070407
- Young-Jin Park, Hui-Sup Cho, "Lung Cancer Tumor Detection Method Using Improved CT Images on a One-stage Detector", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 4, pp. 1–8, 2022. doi: 10.25046/aj070401
- Ayoub Benchabana, Mohamed-Khireddine Kholladi, Ramla Bensaci, Belal Khaldi, "A Supervised Building Detection Based on Shadow using Segmentation and Texture in High-Resolution Images", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 3, pp. 166–173, 2022. doi: 10.25046/aj070319
- Hanae Naoum, Sidi Mohamed Benslimane, Mounir Boukadoum, "Encompassing Chaos in Brain-inspired Neural Network Models for Substance Identification and Breast Cancer Detection", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 3, pp. 32–43, 2022. doi: 10.25046/aj070304
- Haruka Motohashi, Hayato Ohwada, "Interpretable Rules Using Inductive Logic Programming Explaining Machine Learning Models: Case Study of Subclinical Mastitis Detection for Dairy Cows", Advances in Science, Technology and Engineering Systems Journal, vol. 7, no. 2, pp. 143–148, 2022. doi: 10.25046/aj070214
- Janusz Gurzynski, Lukasz Kajda, Marcin Tarasiuk, Tomasz Samotyjak, Zbigniew Stachowicz, Slawomir Kownacki, "Control and Monitoring Systems in Medium Voltage Distribution Networks in Poland – Current Status and Directions of Development", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 6, pp. 112–118, 2021. doi: 10.25046/aj060615
- Seok-Jun Bu, Hae-Jung Kim, "Ensemble Learning of Deep URL Features based on Convolutional Neural Network for Phishing Attack Detection", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 5, pp. 291–296, 2021. doi: 10.25046/aj060532
- Dmitry Petrov, Ulrich Hilleringmann, "Low-Power Primary Cell with Water-Based Electrolyte for Powering of Wireless Sensors", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 5, pp. 267–272, 2021. doi: 10.25046/aj060529
- Natasia, Sani Muhamad Isa, "Cyberbullying Detection by Including Emotion Model using Stacking Ensemble Method", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 5, pp. 229–236, 2021. doi: 10.25046/aj060525
- Osaretin Eboya, Julia Binti Juremi, "iDRP Framework: An Intelligent Malware Exploration Framework for Big Data and Internet of Things (IoT) Ecosystem", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 5, pp. 185–202, 2021. doi: 10.25046/aj060521
- Baida Ouafae, Louzar Oumaima, Ramdi Mariam, Lyhyaoui Abdelouahid, "Survey on Novelty Detection using Machine Learning Techniques", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 5, pp. 73–82, 2021. doi: 10.25046/aj060510
- Dunisani Thomas Chabalala, Julius Musyoka Ndambuki, Wanjala Ramadhan Salim, Sophia Sudi Rwanga, "Application of Geographic Information Systems and Remote Sensing for Land Use/Cover Change Analysis in the Klip River Catchment, KwaZulu Natal, South Africa", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 5, pp. 65–72, 2021. doi: 10.25046/aj060509
- Jianhua Yang, Lixin Wang, Yien Wang, "Enhance Student Learning Experience in Cybersecurity Education by Designing Hands-on Labs on Stepping-stone Intrusion Detection", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 4, pp. 355–367, 2021. doi: 10.25046/aj060440
- Shiwei Zhou, Jiayuan Gong, Leipeng Qie, Zhuofei Xia, Haiying Zhou, Xin Jin, "Driver Fatigue Tracking and Detection Method Based on OpenMV", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 3, pp. 296–302, 2021. doi: 10.25046/aj060333
- Hoang Giang Vu, Thi Thuong Huyen Ma, "Observer-Based Method of Feature Extraction for the Fault Detection of Permanent Magnet Synchronous Motors", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 2, pp. 942–948, 2021. doi: 10.25046/aj0602107
- Binghan Li, Yindong Hua, Mi Lu, "Advanced Multiple Linear Regression Based Dark Channel Prior Applied on Dehazing Image and Generating Synthetic Haze", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 2, pp. 790–800, 2021. doi: 10.25046/aj060291
- Susanto Kumar Ghosh, Mohammad Rafiqul Islam, "Convolutional Neural Network Based on HOG Feature for Bird Species Detection and Classification", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 2, pp. 733–745, 2021. doi: 10.25046/aj060285
- Shahnaj Parvin, Liton Jude Rozario, Md. Ezharul Islam, "Vehicle Number Plate Detection and Recognition Techniques: A Review", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 2, pp. 423–438, 2021. doi: 10.25046/aj060249
- Adelaiye Oluwasegun Ishaya, Ajibola Aminat, Bisallah Hashim, Abiona Akeem Adekunle, "Improved Detection of Advanced Persistent Threats Using an Anomaly Detection Ensemble Approach", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 2, pp. 295–302, 2021. doi: 10.25046/aj060234
- Sk. Md. Masudul Ahsan, Aminul Islam, "Visual Saliency Detection using Seam and Color Cues", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 2, pp. 139–153, 2021. doi: 10.25046/aj060217
- Nasr Rashid, Khaled Kaaniche, "SIFT Implementation based on LEON3 Processor", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 1, pp. 1257–1263, 2021. doi: 10.25046/aj0601143
- Antonio Vitale, Federico Corraro, Nicola Genito, Luca Garbarino, Leopoldo Verde, "An Innovative Angle of Attack Virtual Sensor for Physical-Analytical Redundant Measurement System Applicable to Commercial Aircraft", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 1, pp. 698–709, 2021. doi: 10.25046/aj060176
- Anass Barodi, Abderrahim Bajit, Taoufiq El Harrouti, Ahmed Tamtaoui, Mohammed Benbrahim, "An Enhanced Artificial Intelligence-Based Approach Applied to Vehicular Traffic Signs Detection and Road Safety Enhancement", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 1, pp. 672–683, 2021. doi: 10.25046/aj060173
- Alan A. Jorgensen, Las Vegas, Connie R. Masters, Ratan K. Guha, Andrew C. Masters, "Bounded Floating Point: Identifying and Revealing Floating-Point Error", Advances in Science, Technology and Engineering Systems Journal, vol. 6, no. 1, pp. 519–531, 2021. doi: 10.25046/aj060157
- Aarthi Ramachandran, Amudha Joseph, Shunmuga Velayutham, "Feature Gate Computational Top-Down Model for Target Detection", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 1001–1006, 2020. doi: 10.25046/aj0506120
- Andrea Generosi, Silvia Ceccacci, Samuele Faggiano, Luca Giraldi, Maura Mengoni, "A Toolkit for the Automatic Analysis of Human Behavior in HCI Applications in the Wild", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 185–192, 2020. doi: 10.25046/aj050622
- Khalid Ait Hadi, Rafik Lasri, Abdellatif El Abderrahmani, "Inferring Topics within Social Networking Big Data, Towards an Alternative for Socio-Political Measurement", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 155–159, 2020. doi: 10.25046/aj050618
- Pamela Zontone, Antonio Affanni, Riccardo Bernardini, Leonida Del Linz, Alessandro Piras, Roberto Rinaldo, "Supervised Learning Techniques for Stress Detection in Car Drivers", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 6, pp. 22–29, 2020. doi: 10.25046/aj050603
- Mohammad Mohammad Abdul-Atty, Ahmed Sayed Ismail Amar, Mohamed Mabrouk, "C-Band FMCW Radar Design and Implementation for Breathing Rate Estimation", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 5, pp. 1299–1307, 2020. doi: 10.25046/aj0505156
- Redha Touati, Max Mignotte, Mohamed Dahmane, "A Circular Invariant Convolution Model-Based Mapping for Multimodal Change Detection", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 5, pp. 1288–1298, 2020. doi: 10.25046/aj0505155
- Paul Cabacungan, Carlos Oppus, Gregory Tangonan, Nerissa Cabacungan, John Paul Mamaradlo, Neil Angelo Mercado, "Design and Development of Electronic Sensor and Monitoring System of Smart Low-cost Phototherapy Light System for Non-Invasive Monitoring and Treatment of Neonatal Jaundice", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 5, pp. 1233–1246, 2020. doi: 10.25046/aj0505149
- Khalid A. AlAfandy, Hicham, Mohamed Lazaar, Mohammed Al Achhab, "Investment of Classic Deep CNNs and SVM for Classifying Remote Sensing Images", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 5, pp. 652–659, 2020. doi: 10.25046/aj050580
- Chunlai Yan, Hongxia Li, "Knowledge Mapping of Virtual Academic Communities: A Bibliometric Study Using Visual Analysis", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 5, pp. 493–499, 2020. doi: 10.25046/aj050561
- Hicham Moujahid, Bouchaib Cherradi, Oussama El Gannour, Lhoussain Bahatti, Oumaima Terrada, Soufiane Hamida, "Convolutional Neural Network Based Classification of Patients with Pneumonia using X-ray Lung Images", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 5, pp. 167–175, 2020. doi: 10.25046/aj050522
- Rohith Raj S, Pratiba D, Ramakanth Kumar P, "Facial Expression Recognition using Facial Landmarks: A Novel Approach", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 5, pp. 24–28, 2020. doi: 10.25046/aj050504
- Anouar Bachar, Noureddine El Makhfi, Omar EL Bannay, "Machine Learning for Network Intrusion Detection Based on SVM Binary Classification Model", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 4, pp. 638–644, 2020. doi: 10.25046/aj050476
- Adonis Santos, Patricia Angela Abu, Carlos Oppus, Rosula Reyes, "Real-Time Traffic Sign Detection and Recognition System for Assistive Driving", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 4, pp. 600–611, 2020. doi: 10.25046/aj050471
- Katleho Moloi, Yskandar Hamam, Jacobus Andries Jordaan, "A Support Vector Machine Based Technique for Fault Detection in A Power Distribution Integrated System with Renewable Energy Distributed Generation", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 4, pp. 577–588, 2020. doi: 10.25046/aj050468
- Maroua Abdellaoui, Dounia Daghouj, Mohammed Fattah, Younes Balboul, Said Mazer, Moulhime El Bekkali, "Artificial Intelligence Approach for Target Classification: A State of the Art", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 4, pp. 445–456, 2020. doi: 10.25046/aj050453
- Samir Allach, Mohamed Ben Ahmed, Anouar Abdelhakim Boudhir, "Deep Learning Model for A Driver Assistance System to Increase Visibility on A Foggy Road", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 4, pp. 314–322, 2020. doi: 10.25046/aj050437
- Amal Hadri, Khalid Chougdali, Raja Touahni, "Nonlinear \(\ell_{2,p}\)-norm based PCA for Anomaly Network Detection", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 4, pp. 234–243, 2020. doi: 10.25046/aj050429
- Rizki Jaka Maulana, Gede Putra Kusuma, "Malware Classification Based on System Call Sequences Using Deep Learning", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 4, pp. 207–216, 2020. doi: 10.25046/aj050426
- Ali Al-Rashid, "Composition of Methods to Ensure Iris Liveness and Authenticity", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 4, pp. 130–143, 2020. doi: 10.25046/aj050417
- Ruba Obiedat, "Risk Management: The Case of Intrusion Detection using Data Mining Techniques", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 3, pp. 529–535, 2020. doi: 10.25046/aj050365
- Akram Hatem Saber, Mohd Ayyub Khan, Basim Galeb Mejbel, "A Survey on Image Forgery Detection Using Different Forensic Approaches", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 3, pp. 361–370, 2020. doi: 10.25046/aj050347
- Jesuretnam Josemila Baby, James Rose Jeba, "A Hybrid Approach for Intrusion Detection using Integrated K-Means based ANN with PSO Optimization", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 3, pp. 317–323, 2020. doi: 10.25046/aj050341
- Manh Le Tran, Sunghwan Kim, "Enhanced Collaborative Constellation for Visible Light Communication System", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 3, pp. 259–263, 2020. doi: 10.25046/aj050333
- Sally Almanasra, Ali Alshahrani, "Alternative Real-time Image-Based Smoke Detection Algorithm", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 3, pp. 123–128, 2020. doi: 10.25046/aj050316
- Gillala Rekha, Shaveta Malik, Amit Kumar Tyagi, Meghna Manoj Nair, "Intrusion Detection in Cyber Security: Role of Machine Learning and Data Mining in Cyber Security", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 3, pp. 72–81, 2020. doi: 10.25046/aj050310
- Aditi Haresh Vyas, Mayuri A. Mehta, "A Comprehensive Survey on Image Modality Based Computerized Dry Eye Disease Detection Techniques", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 2, pp. 748–756, 2020. doi: 10.25046/aj050293
- Rabeb Faleh, Souhir Bedoui, Abdennaceur Kachouri, "Review on Smart Electronic Nose Coupled with Artificial Intelligence for Air Quality Monitoring", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 2, pp. 739–747, 2020. doi: 10.25046/aj050292
- Yeji Shin, Youngone Cho, Hyun Wook Kang, Jin-Gu Kang, Jin-Woo Jung, "Neural Network-based Efficient Measurement Method on Upside Down Orientation of a Digital Document", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 2, pp. 697–702, 2020. doi: 10.25046/aj050286
- Evan Kristia Wigati, Gede Putra Kusuma, Yesun Utomo, "Combination of Salient Object Detection and Image Matching for Object Instance Recognition", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 2, pp. 584–591, 2020. doi: 10.25046/aj050273
- C. Namrata Mahender, Ramesh Ram Naik, Maheshkumar Bhujangrao Landge, "Author Identification for Marathi Language", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 2, pp. 432–440, 2020. doi: 10.25046/aj050256
- Dr. Minal Moharir, Karthik Bhat Adyathimar, Dr. Shobha G, Vishal Soni, "Scapy Scripting to Automate Testing of Networking Middleboxes", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 2, pp. 293–298, 2020. doi: 10.25046/aj050238
- Nova Muhammad Ferlansyah, Suharjito, "A Systematic Literature Review of Vessel Anomaly Behavior Detection Methods Based on Automatic Identification System (AIS) and another Sensor Fusion", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 2, pp. 287–292, 2020. doi: 10.25046/aj050237
- Brian Meneses-Claudio, Witman Alvarado-Diaz, Avid Roman-Gonzalez, "Classification System for the Interpretation of the Braille Alphabet through Image Processing", Advances in Science, Technology and Engineering Systems Journal, vol. 5, no. 1, pp. 403–407, 2020. doi: 10.25046/aj050151
- Noor Syahirah Nordin, Mohd Arfian Ismail, Vitaliy Mezhuyev, Shahreen Kasim, Mohd Saberi Mohamad, Ashraf Osman Ibrahim, "Fuzzy Modelling using Firefly Algorithm for Phishing Detection", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 6, pp. 291–296, 2019. doi: 10.25046/aj040637
- Farah Nadia Ibrahim, Zalhan Mohd Zin, Norazlin Ibrahim, "Eye Feature Extraction with Calibration Model using Viola-Jones and Neural Network Algorithms", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 6, pp. 208–215, 2019. doi: 10.25046/aj040627
- Niranjan A, Akshobhya K M, P Deepa Shenoy, Venugopal K R, "EKMC: Ensemble of kNN using MetaCost for Efficient Anomaly Detection", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 5, pp. 401–408, 2019. doi: 10.25046/aj040552
- Michael Santacroce, Daniel Koranek, Rashmi Jha, "Detecting Malicious Assembly using Convolutional, Recurrent Neural Networks", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 5, pp. 46–52, 2019. doi: 10.25046/aj040506
- Antonio Fuduli, Pierangelo Veltri, Eugenio Vocaturo, Ester Zumpano, "Melanoma detection using color and texture features in computer vision systems", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 5, pp. 16–22, 2019. doi: 10.25046/aj040502
- Yuto Yoshizawa, Yutaka Watanobe, "Logic Error Detection System based on Structure Pattern and Error Degree", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 5, pp. 01–15, 2019. doi: 10.25046/aj040501
- Stephen Craig Stubberud, Kathleen Ann Kramer, Allen Roger Stubberud, "Estimation of Target Maneuvers from Tracked Behavior Using Fuzzy Evidence Accrual", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 4, pp. 468–477, 2019. doi: 10.25046/aj040457
- Takahiro Ishizu, Makoto Sakamoto, Masamichi Hori, Takahiro Shinoda, Takaaki Toyota, Amane Takei, Takao Ito, "Hidden Surface Removal for Interaction between Hand and Virtual Objects in Augmented Reality", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 4, pp. 359–365, 2019. doi: 10.25046/aj040444
- Maryam Butt, Golshah Naghdy, Fazel Naghdy, Geoffrey Murray, Haiping Du, "Investigating The Detection of Intention Signal During Different Exercise Protocols in Robot-Assisted Hand Movement of Stroke Patients and Healthy Subjects Using EEG-BCI System", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 4, pp. 300–307, 2019. doi: 10.25046/aj040438
- Priyamvada Chandel, Tripta Thakur, "Smart Meter Data Analysis for Electricity Theft Detection using Neural Networks", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 4, pp. 161–168, 2019. doi: 10.25046/aj040420
- Sohail Akhtar, Adarsh Tandiya, Medhat Moussa, Cole Tarry, "An Efficient Automotive Paint Defect Detection System", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 3, pp. 171–182, 2019. doi: 10.25046/aj040323
- Fernando Hernández, Roberto Vega, Freddy Tapia, Derlin Morocho, Walter Fuertes, "Early Detection of Alzheimer’s Using Digital Image Processing Through Iridology, An Alternative Method", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 3, pp. 126–137, 2019. doi: 10.25046/aj040317
- Hakan Tora, Gursel Karacor, Baran Uslu, "Vowel Classification Based on Waveform Shapes", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 3, pp. 16–24, 2019. doi: 10.25046/aj040303
- Mohammad Ahmar Khan, Sarfraz Fayaz Khan, Taher Alawi Taher Barham BaOmar, Abdul Rahman Mohammed Aqeel Ba Omar, "Development & Implementation of Smart Vehicle Over Speeding Detector using IoT", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 2, pp. 170–175, 2019. doi: 10.25046/aj040222
- Muhammad Aizat Bin Abu Bakar, Abu Hassan Bin Abdullah, Fathinul Syahir Bin Ahmad Sa’ad, "Development of Application Specific Electronic Nose for Monitoring the Atmospheric Hazards in Confined Space", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 1, pp. 200–216, 2019. doi: 10.25046/aj040120
- Viorel Lupu, "Web Authentication: no Password; Listen and Touch", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 1, pp. 84–92, 2019. doi: 10.25046/aj040109
- David Kondru, Mehmet Celenk, Xiaoping A. Shen, "State Estimation based Echolocation Bionics and Image Processing based Target Pattern Recognition", Advances in Science, Technology and Engineering Systems Journal, vol. 4, no. 1, pp. 73–83, 2019. doi: 10.25046/aj040108
- Zheng Xie, Chaitanya Gadepalli, Farideh Jalalinajafabadi, Barry M.G. Cheetham, Jarrod J. Homer, "Machine Learning Applied to GRBAS Voice Quality Assessment", Advances in Science, Technology and Engineering Systems Journal, vol. 3, no. 6, pp. 329–338, 2018. doi: 10.25046/aj030641
- Elena Basan, Alexander Basan, Oleg Makarevich, "Probabilistic Method for Anomalies Detection Based on the Analysis of Cyber Parameters in a Group of Mobile Robots", Advances in Science, Technology and Engineering Systems Journal, vol. 3, no. 6, pp. 281–288, 2018. doi: 10.25046/aj030636
- Tamarafinide Victory Dittimi, Ching Yee Suen, "Modified HOG Descriptor-Based Banknote Recognition System", Advances in Science, Technology and Engineering Systems Journal, vol. 3, no. 5, pp. 354–364, 2018. doi: 10.25046/aj030541
- Satyam Paul, Raheleh Jafari, "Recent Advances in Intelligent-Based Structural Health Monitoring of Civil Structures", Advances in Science, Technology and Engineering Systems Journal, vol. 3, no. 5, pp. 339–353, 2018. doi: 10.25046/aj030540
- Adel Mounir Said, Emad Abd-Elrahman, Hossam Afifi, "Q-Learning versus SVM Study for Green Context-Aware Multimodal ITS Stations", Advances in Science, Technology and Engineering Systems Journal, vol. 3, no. 5, pp. 328–338, 2018. doi: 10.25046/aj030539
- Imad Hasan Tahini, Alex Dadykin, "Proposed System of New Generation LMS Using Visual Models to Accelerate Language Acquisition", Advances in Science, Technology and Engineering Systems Journal, vol. 3, no. 5, pp. 277–287, 2018. doi: 10.25046/aj030533
- Jia-Jing Kao, Chun-Liang Lin, Chih-Cheng Huang, Hau-Shian Jian, "Contactless Power and Bidirectional Data Transmission via Magnetic Field", Advances in Science, Technology and Engineering Systems Journal, vol. 3, no. 5, pp. 226–234, 2018. doi: 10.25046/aj030528
- Mohammed Faeik Ruzaij Al-Okby, Sebastian Neubert, Norbert Stoll, Kerstin Thurow, "Development and Testing of Intelligent Wheelchair Controller for Quadriplegic Patients", Advances in Science, Technology and Engineering Systems Journal, vol. 3, no. 5, pp. 220–225, 2018. doi: 10.25046/aj030527
- Andre Dehne, Nantwin Moller, Thorsten Hermes, "MARWIN: Localization of an Inspection Robot in a Radiation exposed Environment", Advances in Science, Technology and Engineering Systems Journal, vol. 3, no. 4, pp. 354–362, 2018. doi: 10.25046/aj030436
- Abraham Amole, Bamidele Sanya Osalusi, "Textural Analysis of Pap Smears Images for k-NN and SVM Based Cervical Cancer Classification System", Advances in Science, Technology and Engineering Systems Journal, vol. 3, no. 4, pp. 218–223, 2018. doi: 10.25046/aj030420
- Mohamed Abd Elghany Khalifa, Amr Elsayed Emam, Mohamed Ibrahim Youssef, "Performance Enhancement of MIMO-OFDM Using Redundant Residue Number System", Advances in Science, Technology and Engineering Systems Journal, vol. 3, no. 4, pp. 1–7, 2018. doi: 10.25046/aj030401